A World Without Encryption (Video)
Thursday, February 1, 2024
A World Without Encryption (Video)
Saturday, April 30, 2022
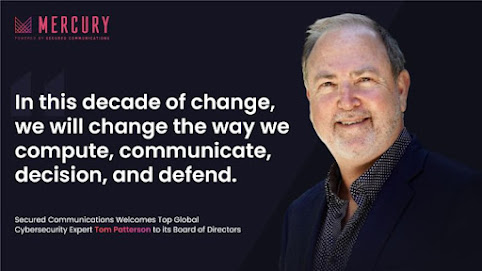
I'm very focused on ensuring that the changes in the way we compute, communicate, decision, and defend that are coming this decade, will be done in a way that contributes to the overall privacy, safety and security of the civilized world. This decade is ushering in artificial intelligence and machine learning, quantum compute and encryption, advanced communications, and entirely new ways to defend this new infrastructure. Much of this change will come from innovative emerging companies that need to be part of the fabric of this new global infrastructure.
To that end, I'm thrilled to announce that I have joined the Board of Directors of Secured Communications Inc, which has built the Mercury Workspace to give enterprises a secure choice for their online collaborations with remote employees, trusted partners, important clients, and evolving ecosystems. Their platform is built upon the latest encryption standard of MLS, which defends against a current threat of 'steal now, decrypt later' that is being weaponized by adversaries around the globe and aimed at companies in all of the 17 critical infrastructure sectors as well as governments around the world.
The Mercury platform provides everything an organization needs for online collaboration including voice, video, conferencing, messaging, and shared files, but with enterprise controlled end-to-end encryption and positive identification. No more worries about your private and sensitive information being monitored and monetized by your collaboration providers, no more worries about someone stealing your data or 'zoom-bombing' your meeting, and no more worries that your most sensitive conversations are the least protected in your enterprise.
I'm excited to roll up my sleeves as a board member to help advise this great group of security leaders in the best way to accelerate their platform to be the go-to service when privacy and security are important in an online collaboration.
Five years ago (2017) I did this podcast on consumer cyber protections, and it's amazing how the advice is just as relevant now, and even more important. While some predictions don't age well ( "I think there is a world market for maybe five computers." - Thomas Watson, President of IBM ) the advice here on doing the basics well will greatly reduce your risk of ransomeware impacts, identify compromise, and theft of assets. Go on, have a listen for old times sake!
https://www.getyourselfoptimized.com/avoiding-cyber-threats-smart-security-tom-patterson/
Saturday, March 19, 2022
Cyber Education isn't just kid stuff. Cross-training executives is also a critical component of our collective success, along with enhanced focuses from K through grey, diversity of all sorts, and mentoring.
Such a pleasure to work with the over 500 executives that attend Wharton Executive Education each year, and focus them on the most critical issues of #cyber #security. Thanks to the great SIFMA SII team and all the executives that participated in my series of security, trust, and resilience lectures.
Friday, May 29, 2020

Dispatches from Davos 2020
- Monday, January 20 article - Themes, styles and manifestos
- Tuesday, January 21 article - Security still top of mind
- Wednesday, January 22 article - Technology’s opportunity in a cohesive and sustainable world
- Thursday, January 23 article - Bring on the night, where the real deals get done
- 23. Januar 2020 - IT Daily article: Botschaften aus Davos 2020: Was die Welt beschäftigt
- Friday, January 24 article - Messages, meanings and more
- Watch the Video from Day 5 (please note: video is very soft; turn up volume)
- January 24 - Tech Accord: Cybersecurity Tech Accord returns to the World Economic Forum
- 25. Januar 2020 - IT Daily: Botschaften aus Davos: Zusammenfassung